Vulnerability scanning is an important but optional component of SOC 2 compliance. However, there are many aspects to consider before diving into SOC 2 vulnerability scanning. Let’s explore what SOC 2 is and the importance of vulnerability scanning in achieving compliance.
Your company is undertaking a compliance process, and you’re likely wondering: what are SOC 2 vulnerability scanning requirements and their significance for an audit?
Achieving and retaining SOC 2 has become a crucial milestone for businesses of all sizes, particularly those operating in the SaaS landscape, to demonstrate to external parties that they maintain stringent measures to protect data and information systems. More often than not, having a SOC 2 report can dictate the success or failure of a business deal or a lower risk score in the supplier onboarding process, highlighting its relevance to many companies as it defines a baseline of confidence in your firm and has a direct impact on your revenue.
Is vulnerability scanning obligatory for a SOC 2 audit to ensure conformity with AICPA’s Trust Services Criteria? This question is commonly asked by companies going through a compliance journey when topics related to information security arise, and the response is occasionally vague due to multiple conflicting data available online regarding this subject.
In this article, we delve into the world of vulnerability scanning, its benefits, and its relevance to compliance with SOC 2, with the intention to support decision-making in your audit and compliance objectives.
What is SOC 2 compliance?
If you have arrived here, chances are you’re already familiar with SOC 2, and you know what it is all about. Nevertheless, for those who aren’t yet well-versed in SOC 2 compliance, this paragraph serves as a very brief intro to the topic.
SOC 2, which stands for Service Organization Controls 2, constitutes a collection of norms that companies must comply with to ascertain that policies and methodologies are established to improve their systems and data security. The American Institute of Certified Public Accountants (AICPA) is the body responsible for this framework. To achieve SOC 2 compliance, firms must demonstrate they possess thorough strategies and sound information security policies. Additionally, they must undergo routine independent evaluations to affirm their systems’ security and privacy controls are in line with the framework.
What are the SOC’s five Trust Services Criteria?
SOC compliance covers five trust service principles:

- Security: This refers to the protection of system resources against unauthorized access. This is the core principle and is included in every SOC 2 examination. Security measures are aimed at preventing potential system abuse, unauthorized removal of data, unauthorized changes to system resources, and system disruption.
- Availability: This refers to the accessibility of the system, products, or services as stipulated by a contract or service level agreement (SLA). The system should be available for operation and use as agreed upon. This principle does not impose full-time availability; the details are based on the agreement between both parties.
- Processing Integrity: This principle is about whether a system achieves its purpose (i.e., delivers the right data at the right price at the right time). Accordingly, data processing should be complete, valid, accurate, timely, and authorized.
- Confidentiality: This principle pertains to data designated as confidential, and it should be protected as agreed upon in the service level agreement (SLA). Confidential data could include sensitive data such as personally identifiable information (PII) or business secrets.
- Privacy: This principle addresses the system’s collection, use, retention, disclosure, and disposal of personal information in conformity with an organization’s privacy notice, as well as with criteria set forth in the AICPA’s generally accepted privacy principles (GAPP).
What is vulnerability scanning?
Vulnerability scanning is a systematic approach to identifying, quantifying, and ranking the vulnerabilities in a system. It’s a cyber health check for your IT infrastructure, designed to uncover any potential weaknesses that could be exploited by attackers.
By identifying these vulnerabilities, organizations can address and patch them before they are exploited, significantly reducing the risk of a security incident. Vulnerability scanning should be done on a regular basis, as new vulnerabilities are continually discovered and added to the databases used by scanners.
While vulnerability scanning is an integral part of cybersecurity, it should not be confused with penetration testing. The two are related but serve different purposes.
What are vulnerability scanning requirements for SOC 2 compliance?
Vulnerability scanning is not an explicit requirement in SOC 2 audits but serves as a substantial adjunct to the framework. It adds depth to your organization’s security practices and provides demonstrable evidence of proactive measures against potential cyber threats.
Even though it’s not a compulsory requirement, vulnerability scanning can aid in fulfilling the subsequent prerequisites criteria CC7.1 from the Trust Services Criteria (System operations) and its points of focus:
- CC7.1: “To meet its objectives, the entity uses detection and monitoring procedures to identify (1) changes to configurations that result in the introduction of new vulnerabilities, and (2) susceptibilities to newly discovered vulnerabilities”
- CC7.1 point of focus: “Conducts Vulnerability Scans — The entity conducts vulnerability scans designed to identify potential vulnerabilities or misconfigurations on a periodic basis and after any significant change in the environment and takes action to remediate identified deficiencies on a timely basis”
While the SOC 2 standard does not directly require vulnerability scanning, it mandates that organizations implement effective controls to ensure system and data security to safeguard customer data. Hence, the incorporation of vulnerability scanning in the security strategy can be perceived as a proactive step in meeting SOC 2 compliance security requirements.
How vulnerability scanning can enhance SOC 2 Trust Service Principles
Vulnerability scanning’s value lies in its potential to augment the five trust service principles of SOC 2. Here’s a closer look at how vulnerability scanning intersects with each of these principles:
- Security: Vulnerability scanning is a crucial tool for detecting and addressing system vulnerabilities, helping organizations demonstrate their commitment to a secure environment.
- Availability: Regular vulnerability scans identify threats that could lead to denial of service attacks, causing system downtime, thereby ensuring consistent system functionality and accessibility.
- Processing Integrity: While not directly tied to vulnerability scanning, system processing integrity can indirectly benefit from it. Scanning helps prevent unauthorized data modifications, supporting accurate and timely data processing.
- Confidentiality: By spotting weaknesses that could lead to unauthorized access to confidential data, vulnerability scanning bolsters data confidentiality.
- Privacy: Vulnerability scanning identifies system vulnerabilities that could compromise privacy, ensuring timely rectification and maintaining the protection of personal information.
It’s true vulnerability scanning isn’t a direct requirement of SOC 2; however, it’s easy to see how it clearly supports the purpose of SOC 2’s trust service principles.
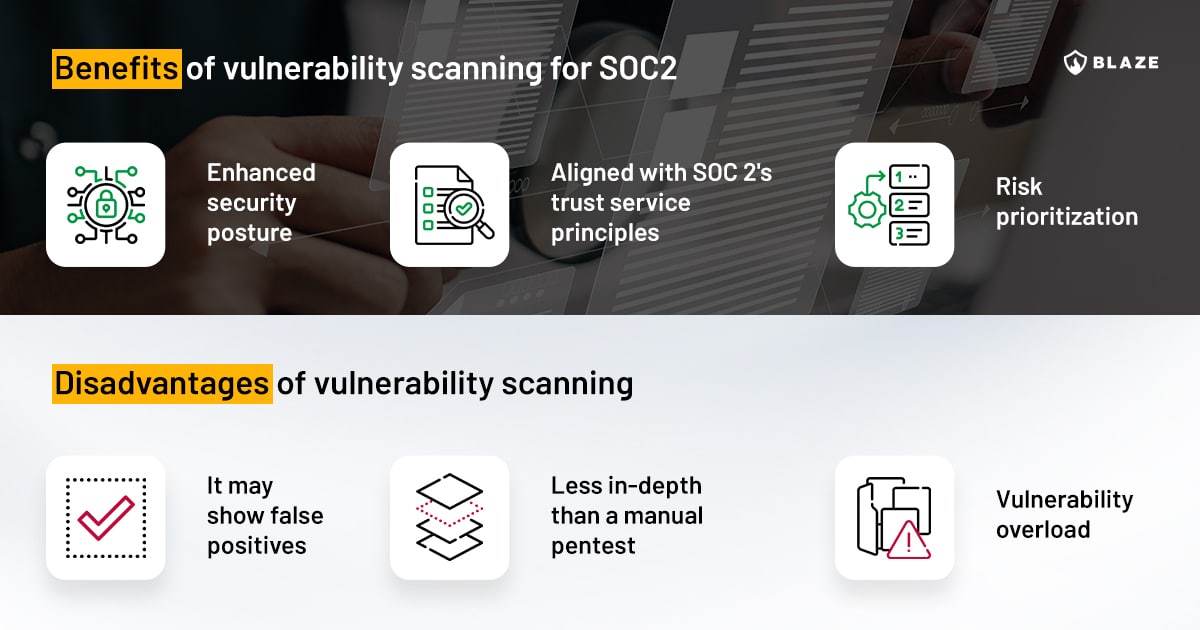
Pros and cons of vulnerability scanning
For compliance reasons or not, it’s important to weigh the benefits and potential challenges associated with vulnerability scanning. Let’s consider both sides of the coin and discuss the benefits and limitations that automated vulnerability scanning can bring.
Benefits of vulnerability scanning
- Enhanced security posture: Vulnerability scanning can identify potential vulnerabilities, and by addressing them, you can greatly enhance the security of your IT environment. Regular scanning enables your organization to stay ahead of potential threats and may help prevent costly and damaging security incidents.
- Supports SOC 2 compliance: Although a vulnerability scan isn’t a specific requirement, its practice aligns well with SOC 2’s trust service principles. Regular vulnerability scanning can be seen as a demonstration of your organization’s commitment to maintaining a secure environment and enhancing trust with your customers and stakeholders.
- Risk prioritization: Vulnerability scanning not only identifies potential threats but can, in some cases, also prioritize them based on their severity to remediate identified deficiencies. This can guide your organization in efficiently allocating resources to address the most serious threats first.
Potential challenges of vulnerability scanning
- False positives: While vulnerability scanners are generally accurate, they can occasionally report false positives, meaning they might identify a threat where there is none. This could lead to unnecessary use of resources in investigating and addressing these supposed threats.
- Only scratches the surface: While vulnerability scanning can identify many potential threats, it isn’t a cure-all solution. Some threats may be missed, especially new or emerging ones that aren’t yet included in the scanner’s database. Additionally, it doesn’t have the same contextual use for the vulnerabilities as a pentest will do, making a vulnerability scan less in-depth than a manual pentest assessment led by an experienced security engineer.
- Vulnerability overload: An automated scanner can identify a large number of vulnerabilities, more than an internal security team can effectively manage or remediate in a reasonable time frame, making it difficult to prioritize what to fix first.
Infographic – SOC 2 vulnerability scanning
Conclusion
While neither vulnerability scanning nor penetration tests are a mandatory component of SOC 2 compliance, their benefits can make them a valuable addition to your compliance strategy. Having a vulnerability management strategy offers a proactive means of identifying and addressing vulnerabilities in your systems and improving your security controls, thereby reinforcing also availability, processing integrity, and confidentiality.
The decision to incorporate vulnerability scanning (and penetration tests) should align with your organization’s unique needs, risk profile, and resources. If you decide to go ahead with these services to augment your audit, selecting a reliable vulnerability scanning service becomes crucial. By weighing these considerations carefully, you can make an informed decision that enhances your security posture, supports SOC 2 compliance, reinforces trust with your stakeholders, decreases cyber risks and ultimately shows proactive measures, as well as detection and monitoring procedures to prevent data breaches.
Blaze has partnered with Vanta and Drata, two of the world’s leading automated compliance platforms, to offer comprehensive assistance to organizations on their SOC 2 compliance path. If your business is contemplating incorporating penetration testing or vulnerability scanning into your SOC 2 audit procedure, reach out to our experts.
FAQ
Does SOC 2 require vulnerability scanning?
SOC 2 does not explicitly require vulnerability scanning. However, vulnerability scanning can support the broader goals of SOC 2 by helping ensure a secure and reliable IT environment.
What is vulnerability scanning, and how does it relate to SOC 2 compliance?
Vulnerability scanning is an automated process to detect system weaknesses that could be exploited by cyber threats. While not a SOC 2 requirement, it reinforces the core SOC 2 focus of a secure and reliable IT environment.
What are the benefits of vulnerability scanning for SOC 2 compliance?
Vulnerability scanning allows proactive threat management, provides evidence of your security commitment, helps prioritize risks, and optimizes IT resource usage, supporting your compliance goals.









