Network Security
Services
Attackers are using increasingly sophisticated methods to try to breach your network. Through real-world attack scenarios simulation, we offer you insights into how adversaries could access your network, so you can prevent them from disrupting your business or accessing business-critical information.
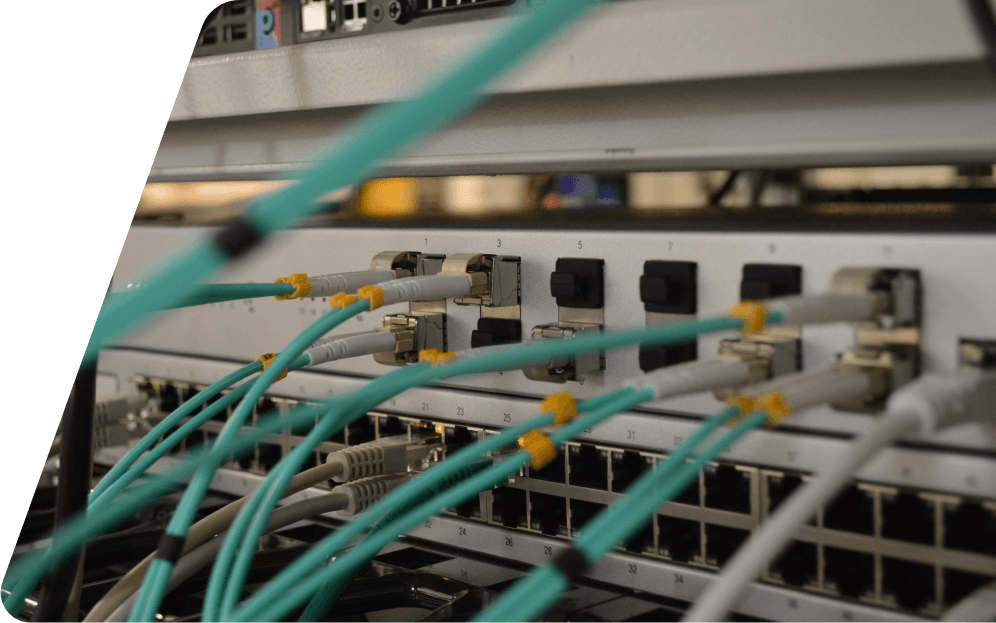
Battle-test your network defenses
and prevent breaches

Internal Pentest
Cyber risks originating from the inside often get overlooked. In fact, most critical vulnerabilities tend to derive from this weak link. Attackers frequently gain access to networks that should be segregated, obtain network credentials, and gain access to servers and file shares hosting corporate secrets and business-critical information.
Blaze’s internal penetration tests thoroughly examine your network infrastructure to uncover gaps and weaknesses that could be exploited by an internal adversary.
External Pentest
Internet-facing services can present risk vulnerabilities that can impact your business and company’s reputation. Our security experts thoroughly scrutinize your internet-facing systems, performing real-life attack scenarios that could lead to unauthorized access. The test aims to evaluate your organization’s defenses and weaknesses against a motivated and persistent external attacker with no access credentials or knowledge about the network environment.

Managed Security Scanning
Our Managed Security Scanning service allows you to continuously improve the defenses of your applications. The assessment enables your company to identify common misconfigurations and vulnerabilities in your network, and address them, improving your overall resilience against attacks.
Assess and reduce risk exposure
Blaze’s penetration testing helps protect your organization from both internal and external threats by identifying and analyzing vulnerabilities and risks. Detecting and preventing possible cyber attacks is key to reducing the impact on your business.
Test your security controls
Our expert security engineers use real-life attack scenarios simulation to test and evaluate the effectiveness of your security controls in response to the security risks and threats your organization might be exposed to.

Manage data access control
Blaze performs extensive testing across your perimeter and internal networks. As we test every angle, we identify vulnerable systems and services that could disrupt your business operations.

Strengthen your security posture with actionable insights
Blaze helps you get a clear perspective of the unique risks that your organization may face. We strive to provide actionable recommendations to help you address the identified vulnerabilities and protect your systems.
Meet regulatory and third-party requirements
Blaze helps your organization pursue the best security practices and stay compliant. We help your company meet third-party, M&A due diligence, and compliance requirements, such as PCI, SOC 2 Type II, ISO 27001, GDPR, HIPAA, CCPA, and others.
Winning approach to application security
We go above and beyond to help
you improve your security
posture

Identify flaws that often fly under the radar
Our methodologies are designed to go beyond common issues listed in OWASP Top 10 to test your unique business logic and operational controls.
Blaze performs tailored penetration tests in a manual fashion, aided by tools and the development of scripts specific to each asset under test. This approach enables us to discover vulnerabilities that often fly under the radar of traditional security testing methods and automated security scanners.

See how your application is exposed to malicious attackers
Our team is composed of seasoned security engineers that are truly passionate about their craft. Our experts are constantly updating their knowledge to keep up with the tactics and techniques that are commonly used by attackers and they focus on offering a real-life attack simulation.

Shift security to the left
By combining security testing with security engineering assessments, we aim to enable you to incorporate security into your DevOps process. By doing so, your developers can learn how to develop more secure code to ensure the security of your apps before they go into production.
Get actionable advice from experts
To help you understand your exposure to risks and threats, our team of experts provides you with a clear description of the vulnerabilities discovered, an assessment of the business impact, and actionable and prioritized remediation guidance to ensure your team can apply effective measures to protect your applications.
Achieve regulatory compliance and meet third-party requests
Blaze helps you achieve and maintain compliance. Our customized reporting is tailored to your specific needs, exceeding even the most demanding requirements. We allow you to meet vendor risk and third-party requirements, M&A due diligence, and compliance requirements such as PCI, SOC 2 Type II, ISO 27001, GDPR, HIPAA, CCPA, and others.
Ready to take your security
to the next level?
We are! Let’s discuss how we can work together to create strong defenses against real-life cyber threats.



