What are DiGA and DiPA?
DiGA (Digitale Gesundheitsandwendungen – or in English, Digital Health Applications), also called “apps on prescription,” are CE-marked medical devices that help patients with the recognition, monitoring, treatment, or alleviation of diseases, injuries, or disabilities. They can be mobile apps, web applications, or other devices whose main functionality is based on digital technology.
In November 2019, the Bundestag allowed physicians in Germany to prescribe digital health applications to their patients. All patients who have statutory health insurance are eligible to receive prescribed health app care. In January 2024, there were 59 DiGA in the BfARM directory. Some examples of DiGA apps are: Deprexis, available as a web app for assisting in the treatment of depression, Endo App for patients suffering from endometriosis, or Elevida – a web app for people with multiple sclerosis.
In October 2022, BfARM published an ordinance establishing requirements for reimbursement of digital care applications (DiPA – Digitale Pflegeandwendungen) intended to support the everyday care of patients. DiPA are intended for use by care recipients and their nurses and carers, including family members – they are not considered health devices but “care assistants.” Manufacturers of said apps and devices are now able to apply to have their products listed in the DiPA directory.
The stakes of keeping patient health data secure
Why DiGA and DiPA manufacturers should prioritize security?
The Federal Office for Information Security (BSI) emphasizes in its technical guideline for manufacturers of e-health applications BSI TR-03161 the importance of protecting patients’ data and the perils of not complying with security requirements. It considers unintentional disclosure of patients’ health data more harmful than some data breaches in the financial sector, as the former can endanger patients’ health, and unlike fraudulent financial operations, it cannot be refunded. The loss of confidentiality is irreversible, and its consequences are severe.
That’s why the regulations and guidelines regarding DiGAs’ security are strict and about to become even more rigorous. The data protection and security requirements for DiPA are expected to follow the ones for DiGA.
Security requirements for Digital Health Applications (DiGA)
To be classified as DiGA and qualify for reimbursement from German health insurance funds, and therefore become readily available to 73 million patients, the device must pass a Fast Track assessment by the Federal Institute for Drugs and Medical Devices (BfArM).
The three-month assessment process checks the app’s general usability, interoperability, user-friendliness, and, finally, its handling of security and data protection.
Annex 1 to the Digital Health Applications Ordinance (DiGAV) specifies medical devices’ requirements regarding data security. Manufacturers of all digital health applications must meet requirements regarding
- Implementing ISMS systems, such as ISO 27001
- Prevention of data leakage
- Authentication
- Access control
- Integration of data and functions
- Logging
- Regular and secure updates
- Safe uninstall
- Hardening
- Use of sensors and external devices
- Use of third-party software
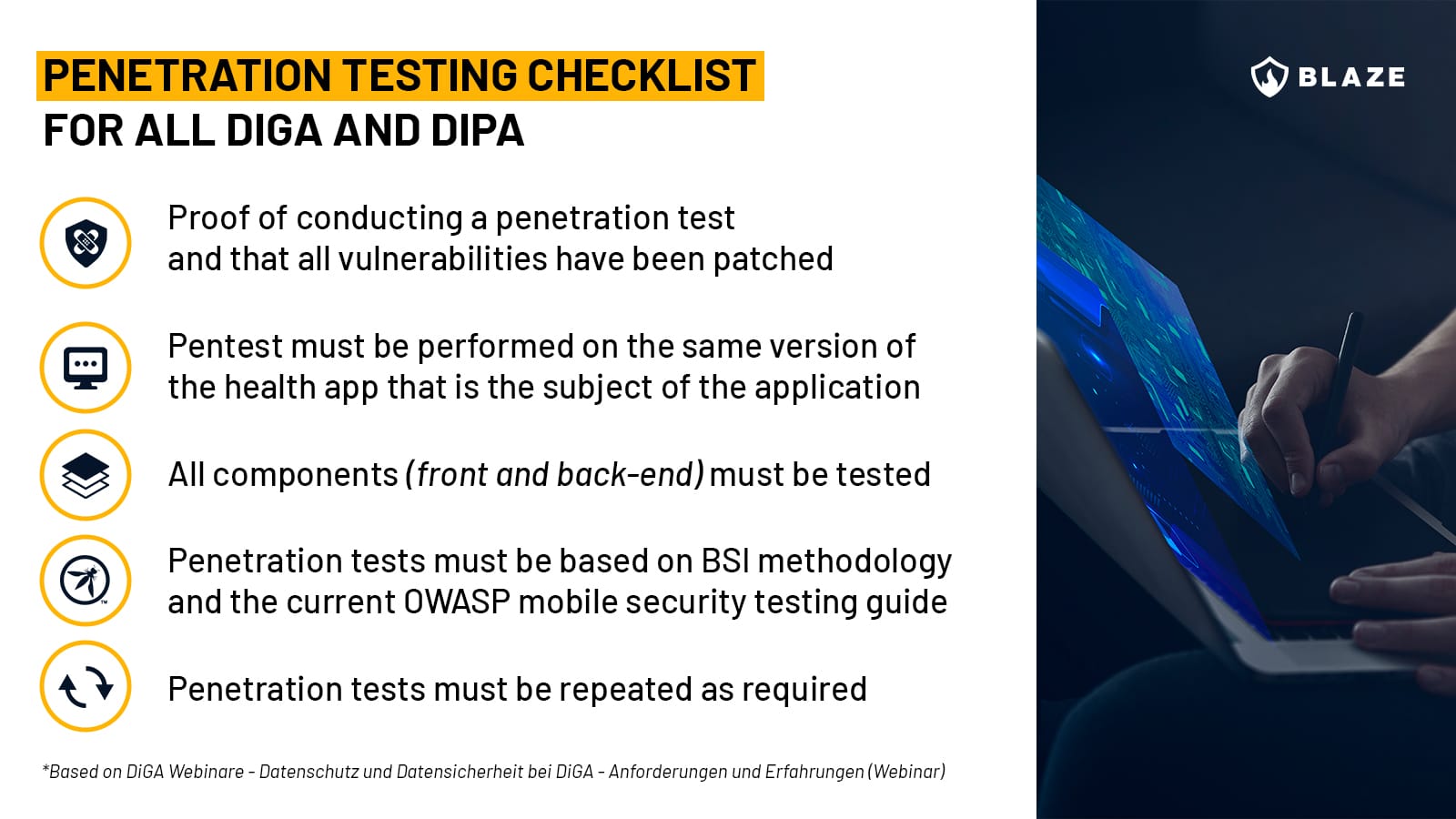
- Penetration testing
According to section 32a of DiGAV Annex 1, all the devices that want to become a digital health application, not only the ones with very high protection requirements, must undergo a penetration test that includes all back-end components and “follows the implementation concept for penetration tests recommended by the Federal Office for Information Security, and – insofar as the applicability is given – also takes into account the current OWASP Top-10 security risks”. The manufacturer is further obliged to “submit appropriate evidence for the implementation of the penetration tests and the elimination of the weak points found on request.”
Digital health applications with very high protection requirements must meet additional requirements regarding:
- Two-factor authentication
- Encryption of stored data
- Measures against DoS and DDoS
- Embedded web services
The specifics of a DiGA pentest
What Annex 1 doesn’t mention is that penetration testing assessments for DiGA and DiPA compliance can sometimes be more nuanced than everyday pentesting. Security engineers performing pentests for digital health applications should have a stronger focus on finding vulnerabilities that may expose patient data, such as IDORs and problems in access control enforcement, and need to be familiar with standards that are specific to the sector, such as HL7, DICOM, FHIR as well as proprietary protocols.
Choosing penetration testing services based on methodologies such as OWASP Top 10, OWASP MASVS, OSSTMM, PTES, and BSI standards (mandatory for DiGA/DiPA) will ensure an in-depth review of the security controls of the platforms and systems in the scope of your audit.
Penetration testing requirements for DiGA Digital Health Apps on Prescription
Certifications required for DiGA
From April 1, 2022, proof of an “information security management system (ISMS) in accordance with ISO 27001 must be submitted.
Since January 1, 2023, a certificate from the BSI must prove that the data security requirements are met.
Since April 1, 2023, data protection requirements must also be met.
The new requirements must be met by the medical apps already listed in the directory and those whose manufacturers only apply for inclusion.
DiGA and data processing outside the EU
In July 2023, the European Commission adopted the adequacy decision for the EU-US data protection framework, according to which personal data can be transferred from the European Union to the USA. However, US companies must sign up to the EU-US framework by agreeing to comply with detailed data protection requirements.
In October 2023, BfArM published its position on data processing outside Germany. Before that, strict regulations applied regarding where health data and personal data may be processed outside of Germany, meaning patient data processing using US-based cloud providers was forbidden. BfArM’s position now states:
“The General Data Protection Regulation (GDPR) generally permits data processing of personal data within the European Union (EU). Processing outside the EU in a so-called third country is permissible if a comparable level of protection exists in the third country (adequacy decision under Article 45 GDPR). The Digital Health Applications Ordinance (DiGAV) limits the location of data processing for the data processed by the DiGA pursuant to Section 4 paragraph 2 DiGAV to the Federal Republic of Germany, the Member States of the EU, the contracting states to the Agreement on the European Economic Area (EEA) and Switzerland.”
“Service providers based in the US may be used for the storage and processing of personal data, provided that they join the EU-US data protection framework, which requires them to comply with detailed data protection obligations”.
Data protection is a rapidly changing topic, and it’s recommended that you consult your trusted compliance officer for up-to-date information.
How to keep digital health apps safe in the long term?
A single pentest and obtaining appropriate certification do not make an app secure in the long term, and BfArM is well aware of it when it stresses that information security should be a process to be anchored in a company. Pentests should be repeated, for example, when new interfaces are added to the internet.
Considering the record levels of cybersecurity breaches that were carried out in Germany last year and the fact that their main targets were critical to society and included healthcare, DiGA and DiPA will have to adhere to very strict security standards if they want to conquer society that has relied on analog healthcare systems longer than most EU countries.
Why is pentesting so important for DiGA and DiPA security?
DiGA has lately attracted the attention of a German hacking collective Zervorschung whose test discovered security vulnerabilities in two health applications that had already been positively verified and listed on BfARM. Critical vulnerabilities included downloading other patients’ data (including username, email address, and details about their health condition) and logging in as a doctor and accessing critical data such as passwords and medical reports.
The apps’ manufacturers fixed the issues after Zervorschung contacted them. Should patients rely on friendly hackers to help secure the apps? No. Broken Access Control vulnerabilities such as the above are often identifiable with a pentest and should have been discovered before the apps were made available to patients. Hopefully, new certification requirements will prevent apps with glaring security issues from reaching patients.
Conclusion
The digitization of Germany’s healthcare system, of which DiGA and DiPA are a part, is one of the most significant current IT operations in Europe, and at the heart of it lies patient data protection.
The trust in health apps on prescription is slowly growing. In 2022, over a third of doctors prescribed digital health apps, and a further 13.9 percent wanted to do so in the near future. Yet, 34.7% of doctors still do not want to use DiGA. In this context, ensuring security compliance is not only a matter of meeting requirements for reimbursement but an important step in building trust among doctors and patients who still hesitate to fully embrace the possibilities that these applications present.








