It might seem, to many, that the financial sector is the one most commonly targeted by cybercriminals; however, according to the European Union Agency for Cybersecurity (ENISA) Threat Landscape 2022 report, it is only the fifth one, after public administration, digital service providers, general public and services.
Despite ranking fifth, the impact of cyberattacks on financial and banking institutions parallels the damage seen in government sectors. The financial sector is one where the ripple effects of a successful breach are felt strongly, not just in terms of financial losses but also the degradation of trust, tarnishing the reputation of the institution in the eyes of its customers and the public at large. The majority of these high-impact digital incidents are precipitated by a particularly menacing type of malware—ransomware.
As we delve further into this blog post, we will examine the major cyber threats facing the financial sector, take a look at who some of the threat actors are, and present effective strategies for mitigating the risk and potential damage from these attacks. By understanding the evolving cyber threat landscape, financial institutions can better safeguard their systems, data, and reputation.

Trends in cyberattacks on the financial sector
Cyberattacks in the financial sector were on the rise in 2022, with ransomware, aided by the Ransomware-as-a-Service crime model, remaining the most significant threat.
According to VMware’s Modern Bank Heists 5.0 report from 2022, 74% of the surveyed financial firms were targeted by ransomware attacks, and 65% ended up paying the ransom.
Other statistics, such as the latest BSI report from Germany, also show that in many instances paying the ransom doesn’t guarantee successful regaining of the lost assets and that double extortion is now the norm. We will discuss Ransomware-as-a-Service (RaaS) model later on.

Financial services cyber threats
From major banks to local credit unions, organizations in the financial services sector face an evolving landscape of digital threats that seek to undermine their security, compromise sensitive data and disrupt their operations. Understanding these threats is the first step towards developing and implementing effective countermeasures to safeguard these institutions and the customers they serve. Let’s take a look at the biggest cyber threats for finance sector in 2023.
Malware and ransomware attacks
Ransomware is a type of malicious software that, once activated, encrypts a victim’s files and often spreads to shared network drives. The files remain encrypted until a ransom is paid to the attackers, who then ideally provide a digital key that decrypts the files. Recent high-profile examples of ransomware attacks include the cyber criminal Russian group Cl0p’s attack on multiple European and US institutions. The group exploited, among other security issues, a vulnerability in the MOVEit file transfer app used by many financial services firms and governments.
How ransomware works
The typical ransomware attack occurs through one of the following vectors:
- Exploiting System Vulnerabilities. This method is responsible for nearly half of the ransomware attacks, according to Palo Alto research.
Cybercriminals often use ransomware to exploit unpatched or outdated software vulnerabilities. They scan the internet for systems running software known to be susceptible to specific exploits, and when they find one, they use the exploit to inject the ransomware directly into the system.
This seems to be Cl0p’s modus operandi. Early in 2023, the group exploited a vulnerability in GoAnywhere MFT and, more recently, a zero-day vulnerability in MOVEit, which it was testing at least for two years before the attack.
In fact, there is research suggesting that ransomware mostly exploits old vulnerabilities.
- Brute-force credential attacks: One of the oldest types of attacks is still responsible for around 20% of ransomware attacks. A brute-force is a trial-and-error method, automated assisted, used to obtain information such as passwords and usernames. In this type of attack, automated software is used to generate a large number of consecutive guesses of the value of the desired data.
Brute-force attacks can be largely mitigated by implementing an account lockout policy, combined with multi-factor authentication for added security. If a password is not guessed within a certain number of attempts, the account is locked, thereby nullifying the attack. However, this can lead to denial-of-service if the account locked out is a system account, and can lead to more work for IT departments in unlocking accounts.
- Phishing: When an unsuspecting employee clicks a link or opens an attachment from a seemingly legitimate email. Phishing is responsible for the initial access of around 12% of ransomware attacks, according to the research above.
- Previously compromised credentials: The credentials may have been compromised in a number of ways. Perhaps they were exposed in a previous data breach, obtained through a phishing attack, bought from a dark web marketplace, or guessed through a brute-force attack.
Once an attacker has these valid credentials, they can log into the targeted system as if they were the legitimate user. This is especially dangerous if the compromised credentials belong to a user with high-level permissions or administrative access. Palo Alto says this vector is used in around 8% of ransomware attacks.
- Internal threats: Disgruntled current or ex-employees and other insiders with legitimate access to the system are responsible for around 8% of ransomware attacks.
- Malvertising or malicious advertising: Malvertising, or malicious advertising, is a technique that uses online advertising to spread malware, including ransomware. Malvertisements can lead a victim to malicious websites or automatically download malware onto a user’s computer or network. The insidious thing about malvertising is that it can occur on legitimate, popular websites without any knowledge of the site’s owner and the user. While not the most common attack vector, it is still a risk for financial institutions.
While we are at malware and ransomware, it is worth addressing some recent hype about ChatGPT’s potential for writing malicious code, with some claiming it will lead to an increase in malware attacks.
While Large Language Models may aid cyber criminals in social engineering attacks and phishing attacks in particular, helping to create credible emails and messages, ChatGPT-written malware lacks the sophistication needed to avoid detection and is not the most potent tool criminals have at their disposal – especially since cyber attackers have quite easy access to a much more powerful and convenient tool, which brings us to the next item on the list of threats for the global financial system.
Ransomware-as-a-Service (RaaS)
A relatively new development in the world of cybercrime, yet already well established, is Ransomware-as-a-Service (RaaS). This model operates much like legitimate Software-as-a-Service (SaaS) business models. In this case, however, the service being provided is ransomware attacks.
RaaS providers sell or rent ransomware software to other criminals who then carry out the attacks. These providers often offer customer service and technical support, helping their criminal customers to maximize the impact of their attacks. The RaaS provider typically takes a percentage of the ransom collected as payment for their services.
This model allows individuals with limited technical skills to carry out sophisticated ransomware attacks. It also means that detecting and stopping these attacks is becoming increasingly difficult as the software and tactics continue to evolve.
German BSI (Federal Office for Information Security) currently considers RaaS LockBit the biggest threat in Germany and worldwide.
It’s important to note that there is no guarantee that paying a ransom will result in your data being decrypted. This uncertainty, combined with the potential financial loss and reputational damage, makes ransomware, especially RaaS, a significant threat to the financial sector.
Social engineering/Phishing attacks
Social engineering attacks present a formidable threat to financial institutions. They exploit the human factor, often regarded as the weakest link in the cybersecurity chain. In these types of attacks, cybercriminals manipulate employees into disclosing sensitive information or performing actions that compromise security, typically by masquerading as a trustworthy entity or person.
Social engineering tactics such as phishing, spear phishing or quid-pro-quo attacks are often used in combination with other hacking methods, for example, to gain initial access to the systems and a foothold into a corporate network.
DDoS and Ransom Denial of Service (RDoS) attacks
DDoS attacks
In a Distributed Denial of Service (DDoS) attack, multiple systems, usually infected with a Trojan, are used to target a system causing a Denial of Service attack. The main goal of such an attack is to make a machine, network, or service unavailable for its intended users by overloading its network or servers with a flood of internet traffic.
DDoS attacks can cause serious disruptions to these banking and financial systems by overwhelming their internet-facing infrastructures and rendering their services inaccessible. These attacks can be costly both in terms of financial loss and loss of trust and reputation.
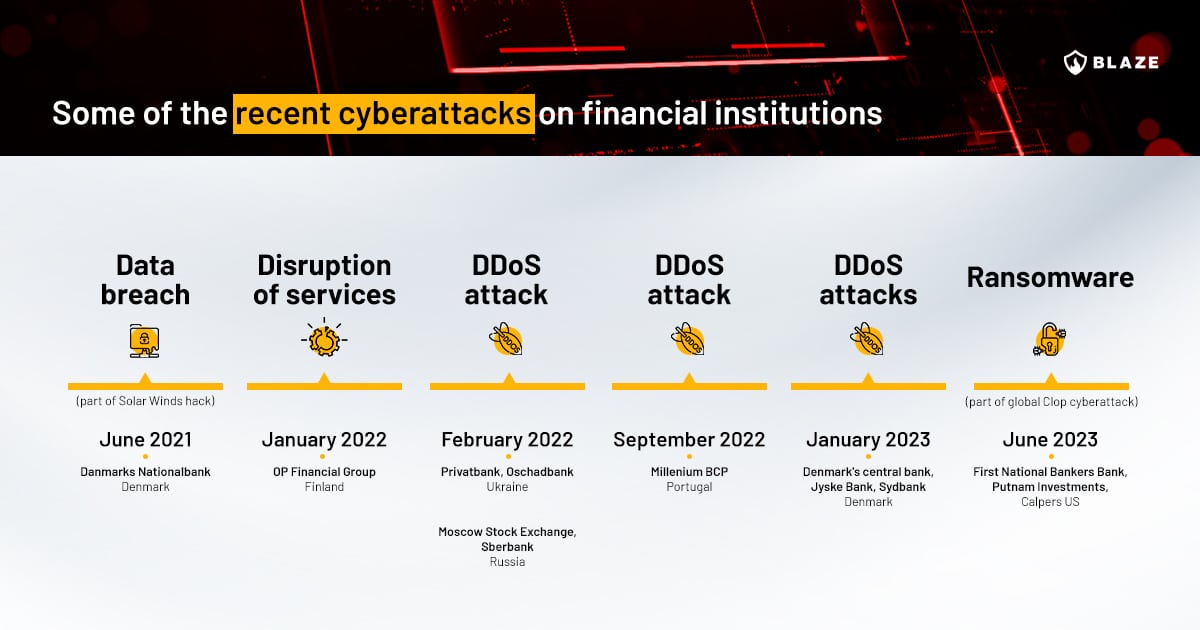
In January 2023 Denmark’s Central Bank, Jyske Bank and Sydbank all suffered DDoS attacks.
What are the most common reasons behind DDoS attacks on financial services firms?
Extortion: Cybercriminals might launch a DDoS attack to demand a ransom from the target institution, threatening to incapacitate their services unless the ransom is paid.
Diversion: Sometimes, DDoS attacks are used as a smokescreen for other malicious activities. While the security team is busy dealing with the DDoS attack, the attackers exploit other vulnerabilities to carry out data or financial theft.
Ideological reasons: Hacktivists may use DDoS attacks to make a political statement or to damage institutions they perceive as harmful or unethical.
Business competition: Unscrupulous businesses might use DDoS attacks to harm their competitors and gain a market advantage.
Revenge: Disgruntled employees or customers might launch a DDoS attack as a form of revenge.
RDoS attacks
Ransom Denial of Service (RDoS) attacks represent a novel and potent vector of cyber threats in the financial sector. Essentially, RDoS operates by first identifying susceptible systems, launching an attack, and ultimately demanding a ransom to cease the onslaught.
These attacks can take one of two forms: they may initially launch an attack and then demand a ransom to halt it, or they may begin with an extortion demand, supported by a minor-scale DoS attack as proof of their intent. The latter scenario can prove more alarming than traditional DDoS attacks as they may be carried out even if the attacker lacks substantial resources.
RDoS integrates multiple attack methods such as Denial of Service, ransomware, and identity spoofing, creating a multifaceted and intricate threat. According to EUROPOL’s Internet Organised Crime Threat Assessment, DDoS attacks followed by ransom demands have resurfaced, with a notable uptick in high-volume attacks. These RDoS attacks have been aimed at internet service providers, financial institutions, and small to medium-sized businesses. The widespread reliance on online services enhances their success rate.
RDoS attacks have expanded their assault perimeters to include not only the direct victims but also their clients, business partners, and employees. After exfiltrating data from victims and threatening to leak it, attackers now coerce victims into paying ransom by launching multi-pronged threats, including denial of service, exposure of confidential data, and implicating affiliated partners.
Supply chain attacks
Supply chain attacks and island hopping can pose a serious threat to banks and financial institutions, which often have numerous connections with other entities such as insurance companies, vendors, service providers, and other banks. Island hopping is a cyberattack strategy where an attacker infiltrates a network in order to attack another, more valuable target. The term “island hopping” is used to depict how attackers seek to move from one system (or “island”) to another to ultimately reach their final objective.
This approach has a number of advantages for the attacker. By compromising a less secure system first, they can use it as a launching pad to infiltrate the primary target. This can make it harder to detect and prevent the attack, since the secondary system might be trusted by the primary target or may not have as robust security measures in place.
Island hopping is not limited to network and system exploitation. It can also be seen in the context of email account compromise, where an attacker compromises one email account to send malicious emails to other accounts.
Some recent examples of supply chain attacks include Operation Cloud Hopper‘s cyberespionage campaign by China-sponsored hackers and the attack on Lattitude Financial in Australia.
According to VM’s Modern Bank Heists Report, 60% of financial organizations observed an increase in island hopping attacks in 2022.
Who are the threat actors?
While a large chunk of cyber attacks on financial institutions is state-sponsored, for example North Korea’s Lazarus group attacks, there are plenty of smaller criminal groups who specialize in attacks on financial institutions.
In the US, according to the most recent report by FinCEN (Financial Crimes Enforcement Network), out of 793 ransomware-related incidents reported to FinCEN in the second half of 2021,
75% (or 594) had a nexus to Russia, its proxies, or persons acting on its behalf. (…) Russia-related ransomware variants accounted for 69% of ransomware incident value, 75% of ransomware-related incidents, and 58% of unique ransomware variants reported for incidents in the review period. All of the top five highest-grossing ransomware variants in this period are connected to Russian cyber actors.
So who are some of the threat actors targeting financial institutions?
- LockBit – ransomware group and ransomware-as-a-service provider. The most active ransomware group in 2022, responsible for about 1,700 attacks (since 2020), according to the FBI. They operate mostly in the US, Canada, New Zealand and Australia.
- GALLIUM – Chinese state-sponsored group, active since at least 2012, primarily targeting telecom companies, financial institutions, and government entities in several regions of the world.
- FIN7 (aka Carbanak) – active international cybercriminal group that first emerged in 2013. It has targeted Russian and Ukrainian banks, retail firms and hospitality organizations in Europe, the US and Japan.
- Lazarus – considered by the FBI to be a state-sponsored North Korean group, they are responsible for attacks on banks in Ecuador, Vietnam, Poland, Mexico, Bangladesh, and Taiwan. They are allegedly the group behind the infamous WannaCry attack.
- Death Stalker – cyber mercenary group targeting law firms and financial institutions
- Silence – consists of two Russian-speaking security professionals whose aim is to target the financial services industry. After a massive phishing campaign targeting Russian banks in 2018, the group expanded its operations to include attacks on banks in Central Asia, Ukraine, India, South Korea, the UK, Australia and Bangladesh. Likely located in Russia.
- Opera1or – French-speaking group whose main victims are financial services, banks, mobile banking services and telecom companies, mostly in Africa but also South America and Bangladesh. In July 2023, members of this cybercrime gang were arrested by law enforcement.
- Cl0p, aka TA505 – Russian-based group operating as a RaaS, initial access broker (IAB) and as a large botnet operator specializing in financial fraud and phishing attacks. According to CISA, TA505 compromised more than 3,000 organizations in the US and 8,000 globally.
- Killnet – Pro-Russian hacktivists recently responsible for the attack on European Investment Bank (EIB), affecting the availability of its website.
Inactive/Dismantled groups
The more notoriety criminal groups gain, the bigger the chances their members will eventually have to face criminal charges. Several big ransomware groups have been dismantled in the past few years. They do have a tendency, however, to regroup and reappear. Especially the individuals operating from politically isolated countries, such as North Korea and now Russia, are harder to track and persecute.
Some of the recently dismantled ransomware gangs include:
- Emotet – taken down in January 2021
- RaaS DarkSide – disbanded after the cyber attack on Colonial Pipeline
- RaaS REvil – disappeared after the cyber attack on Kaseya VSA. Now apparently active again as part of Darknet Parliament (together with Killnet and Anonymous Sudan)
- Conti syndicate – fragmented in May 2022
What can financial institutions do to minimize their cyber risk?
While it is not possible to prevent cyber attacks, there is a lot of financial firms can do to significantly minimize their inherent cyber risk and bolster their security posture – from regular security assessments to employee security awareness training empowering the human element of the security chain. Here are some of the most effective measures against financial sector cyber threats.
- Employee security awareness training
- Incident response planning and testing
- Regular security assessments, including vulnerability scanning and thread-led pentesting, to identify and address any weaknesses in the security infrastructure
- Purple team engagements
- Network segmentation: Separate critical systems and sensitive data from the rest of the network
- Enable multi-factor authentication
- Implement robust access and identity management procedures
Main cyber threats in fintech
The financial technology sector faces its own unique set of threats. While fintech offers innovative solutions that reshape our approach to personal and business finance, these novel platforms, tools, and services often attract the attention of malicious actors keen to exploit emerging vulnerabilities.
Given the revolutionary nature of fintech, these threats often target areas less prevalent in the conventional banking sphere, such as API security, mobile app vulnerabilities, and cloud storage risks.
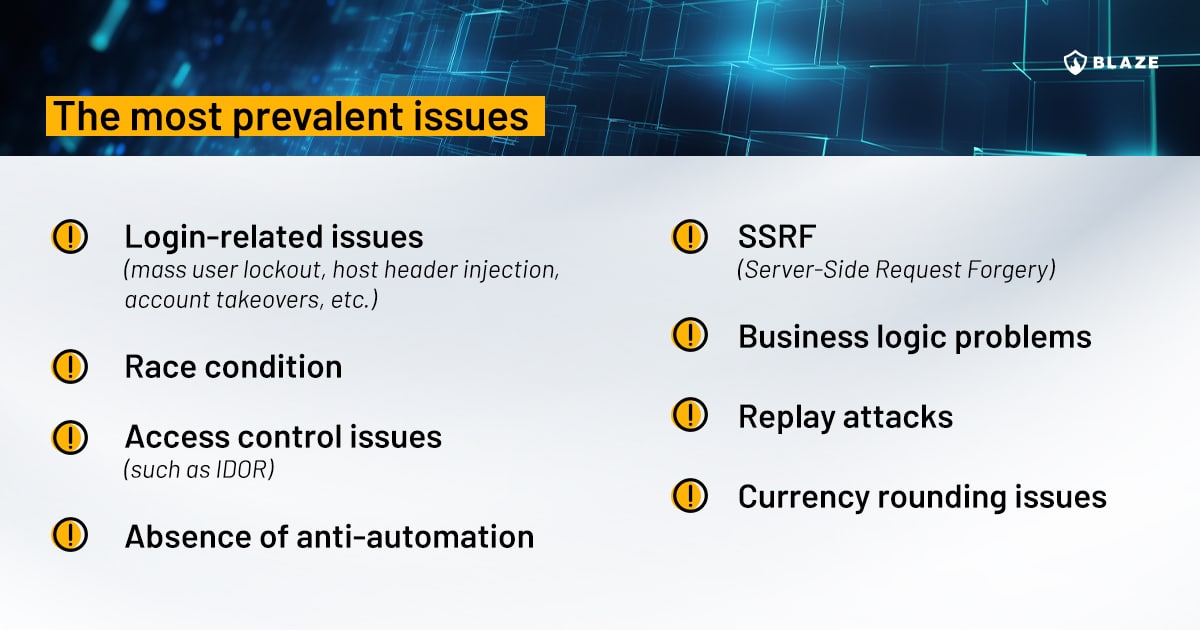
The following table will highlight some of the most prevalent vulnerabilities that we at Blaze discover during penetration tests on fintech applications.
What are the governments doing?
Government agencies and financial authorities across the world are stepping up their regulations to improve the security of their critical infrastructure, financial sector including. Regulations such as DORA in the EU plan to address such issues within the financial system as supply chain security, financial services information sharing, and testing requirements.
The US Securities and Exchange Commission has proposed a new rule on cybersecurity risk management that would impose on the covered entities the obligation to immediately report the occurrence of significant cybersecurity incidents and to improve transparency with respect to cybersecurity risks.
Some governments run stress tests on financial institutions, challenging their resilience to cyber-attacks. In April 2023, Australia launched a war-game exercise to test how its biggest banks and financial services companies would respond to a major cyberattack.
Finally, penetration testing frameworks such as the Bank of England’s CBEST and TIBER-EU in the European Union are created with the aim of increasing the standards of penetration testing required for financial institutions.
Recent cyber attacks in the financial industry
DDoS attacks and ransomware remain the biggest threats to banks and other financial institutions.
Conclusion
Financial organizations find themselves in the crosshairs of increasingly sophisticated cyber threats. Ransomware, DDoS attacks, RaaS, phishing attempts and social engineering tactics continue to pose significant challenges to these institutions. This myriad of threats relentlessly seeks to exploit any vulnerability – from technical loopholes in system security to human errors and oversights.
It’s crucial to remember that these threats are not merely hypothetical but rather have manifested in countless incidents worldwide, causing substantial financial losses and reputational damage. Especially in light of emerging threat actors and the war in Ukraine, remaining vigilant and informed about these threats is absolutely essential not only for financial institutions themselves but for society as a whole.








