The landscape of cyber security insurance has evolved in the last couple of years. Factors such as the increased activity of state-sponsored attacks resulting from the geopolitical situation, increased ransomware and supply chain attacks, and now Ransomware-as-a-Service, influence the availability, the type of coverage offered and the pricing of cyber security insurance policies.
In this blog post, we will discuss the ideal cyber insurance coverage, which common exclusions to look out for, factors influencing the pricing of insurance premiums, and we will provide a checklist for a robust cybersecurity posture that will help your organization to get a payout from your insurance policy.
What is cyber insurance?
Cyber insurance, also known as cyber risk insurance or cyber liability insurance coverage, is designed to help an organization mitigate risk exposure by offsetting costs involved with recovery after a cyber-related security breach or similar events.
Typically, cyber insurance covers the expenses of first parties as well as claims by third parties. The former might include loss or corruption of data, extortion attempts, business interruption, network downtime, crisis management activity related to re-establishing the reputation of the brand, and legal fees related to the incident. The latter might involve legal claims for damages due to exposed information, such as intellectual property, privacy violations, data leakage, and errors and omissions in services.
Why is cyber insurance necessary?
The increasing reliance on technology in business, coupled with the rising sophistication and frequency of cyber-attacks, makes cyber insurance a critical component of a company’s risk management strategy. Here are a few reasons why cyber insurance is necessary:
- Financial Protection: Recovering from a cyber-attack can be costly. Expenses can range from incident response services and forensic investigations, public relations efforts, notification and protection services for customers, to lawsuits and regulatory fines.
- Business Continuity: A significant cyber-attack can interrupt your business operations, leading to loss of revenue. A good cybersecurity insurance policy can help cover the loss of income during this interruption.
- Reputation Management: After a cyber breach, businesses often need to invest in public relations efforts to restore their public image.
- Regulatory Compliance: In many jurisdictions, regulations require companies to take certain actions when they suffer a data breach. This may include notifying customers or paying fines.
- Increasing Threat Landscape: The risk of cyber threats is growing, with criminals continually evolving their methods of attack. Cyber insurance provides a safety net against these unpredictable and evolving threats.
- The Inadequacy of Traditional Insurance: Traditional business liability insurance does not typically cover cyber risks, leaving a gap that cyber insurance fills.
- Limited Resources: Small and medium businesses might not have the resources to manage and mitigate all cyber risks, making cyber insurance an essential tool to protect their business.
What coverage to look for in a cyber insurance policy?
The coverage of your policy will, of course, depend on the type of your business, its size, the industry it operates in and other factors.
What should cyber liability insurance cover:
- Data breaches (data recovery, the costs of notifying affected parties, security fixes, legal costs of incidents involving theft of personal information)
- Cyber attacks
- Cyber attacks on your data held by vendors and other third parties
- Cyber extortion (ransom payment and cleanup costs)
- Business interruption costs
- Reputation protection (public relations costs)
- A lawsuit or regulatory investigation
- Terrorist acts and acts of war
Include first-party and third-party coverage
First-party coverage guards your data and typically includes costs for legal counsel, data recovery, customer notifications, business interruption, crisis management, cyber extortion, fraud, forensics, and incident-related fines.
Third-party coverage protects against liability from claims, covering payments to affected consumers, litigation costs, claim and settlement expenses, defamation, copyright or trademark infringement, and other related damages. Understanding these aspects of your cybersecurity insurance policy can help your business achieve optimal protection.
Common cyber liability insurance policy exclusions
Like all insurance policies, cyber insurance policies also have exclusions or specific situations and activities that are not covered under the policy. These exclusions vary from policy to policy and insurer to insurer, but some of the most common ones include the following:
- Bodily Injury and Property Damage: While a cyber insurance policy will cover losses related to data and digital assets, it generally won’t cover bodily injury or physical property damage. Those are usually covered under general liability or property insurance.
- Intentional Acts: Most cyber insurance policies exclude coverage for acts that are found to be intentionally committed by the policyholder. This includes intentional illegal activities, fraudulent acts, or willful misconduct.
- Unencrypted Devices: Some policies may not cover losses that occur from unencrypted devices. Encryption is a standard security measure, and insurers often require policyholders to take such basic steps to protect their data.
- War and terrorism: Some cyber insurance policies still have exclusions for acts of war, terrorism, or actions by government agencies. This would include state-sponsored cyber attacks.
When US-based Mondelez company became a victim of a likely Russian state-sponsored NotPetya attack in 2017, its cyber insurance provider Zurich American Insurance Company refused to pay for the expenses resulting from the attack ($100 million), citing the war exclusion clause. Mondelez filed a lawsuit against Zurich for failing to deliver on its contractual obligations. The parties eventually settled in 2022; neither disclosed the settlement details. - Infrastructure Failures: Coverage often excludes losses due to utility or infrastructure failures, such as a power outage or telecom/internet downtime, that are not a result of a cyber event.
- Software and Hardware Upgrades: Costs associated with upgrading hardware or software after a cyber incident are generally not covered. This is because they’re seen as part of the normal costs of doing business.
- Late Reporting: If a company doesn’t report a claim or incident within the time frame specified in the policy, the insurer may refuse coverage.
- Non-Compliance with Reasonable Security Measures: If a company fails to maintain reasonable security measures, such as keeping its software updated or its firewalls active, a claim might not be covered.
It’s important for companies to carefully review their cyber insurance policies to understand what is and isn’t covered. It’s also a good idea to work with a knowledgeable broker or legal counsel to ensure the policy meets the company’s specific needs. Companies can often negotiate with insurers to narrow or eliminate certain exclusions.
How is cyber insurance calculated?
The calculation of cyber insurance premiums is a complex process that involves an assessment of multiple factors. Just like any other type of insurance, it involves an analysis of the risk associated with providing the coverage. Here are some of the primary factors that influence cyber insurance costs:
- Industry Type: Some sectors are more vulnerable to cyber attacks than others. Businesses in healthcare, finance, and retail, for instance, often face higher risks due to the sensitive data they handle, leading to higher premiums.
- Company Size: Larger companies may face higher premiums as they typically have more data and broader attack surfaces. However, they may also have more robust security, which could help lower premiums.
- Type and Sensitivity of Data: Companies that handle more sensitive information, like credit card details, health information, or personally identifiable information (PII), are generally considered at higher risk.
- Security Posture: The company’s existing cybersecurity infrastructure and practices significantly impact the cost of cyber insurance. This includes firewalls, encryption, intrusion detection systems, regular audits, employee training programs, incident response plans, and more. Regular vulnerability assessments and penetration tests can demonstrate a company’s commitment to cybersecurity and reduce the premium.
- Past Claims and Breaches: If the company has a history of many cyber incidents or claims, the insurer may consider it a higher risk, which could increase the premium.
- Cyber Risk Management Practices: This includes the measures a company takes to mitigate cyber risk, such as using up-to-date software, regular patching, having a disaster recovery plan, conducting employee cybersecurity training, etc.
- Policy Limit and Deductible: Just like any other type of insurance, higher policy limits and lower deductibles will lead to higher premiums.
- Third-Party Assessments: Insurers may also use assessments from third-party cybersecurity rating companies to determine a company’s security posture. These companies analyze a wide array of security factors and give the company a cybersecurity score.
Because every company’s situation is unique, the insurer typically customizes the policy and the premiums to the specific applicant. It’s also worth noting that as the cyber insurance market matures and more data about cyber threats becomes available, the calculations insurers use to determine premiums are likely to become more refined.
Risk assessment and cyber insurance
Insurers perform risk assessments on companies seeking cyber insurance by evaluating several factors to gauge their level of cyber risk. The goal is to understand the potential exposure to cyber threats, the current state of the company’s cybersecurity measures, and the potential financial impact of a cyberattack. Here are some of the key steps involved:
Application Form: Initially, insurers provide an application form asking about the company’s operations, the type and amount of data they handle, existing cybersecurity measures, previous cyber incidents, and more. The responses form a basis for the initial risk assessment.
Here are some sample questions from the survey used by The Howden Group, that can give you an idea of what kind of security measures insurers expect you to have:
- Do you run simulation games by assuming you have been attacked by a hacker?
- Are critical vulnerabilities (CVSS Base Score ≥ 9.0) patched regularly or fixed by official workarounds?
- Is multi-factor authentication (MFA) used for all internal access by system administrators? ( It should not be possible to bypass the MFA solution by using admin access tools, such as PsExec or Remote Powershell)
- Is your corporate network divided into different segments secured by firewalls to separate critical from non-critical segments (e.g. IT/OT, sensitive data processing)?
- How many unsupported/end-of-life systems are in use?
- Do you use network security technologies for attack detection and defense? (Intrusion Detection / Intrusion Prevention, Endpoint Detection & Response, Extended Detection and Response, Other)
Independent Assessments: In many cases, insurance companies will use independent cyber risk assessment firms that specialize in determining a company’s cyber risk profile. These third-party assessments can help provide an unbiased view of the company’s cybersecurity posture.
In-house Cyber Risk Assessments: Some insurance companies have in-house teams that specialize in cyber risk assessment. These teams can conduct a comprehensive risk assessment, which might include vulnerability scanning, penetration testing, and social engineering testing.
Review of Policies and Procedures: Insurers often review a company’s cybersecurity policies and procedures, including the incident response plan, business continuity plan, and data breach notification procedures. This can give insurers an idea of how well a company can respond to a cyber attack and minimize the damages.
Employee Training and Awareness Programs: Companies that invest in regular employee training about cyber threats and safe practices often pose a lower risk. Insurers may ask about these programs during the assessment.
Review of IT Infrastructure: Insurers may request details about a company’s IT infrastructure, including the use of firewalls, antivirus software, encryption, intrusion detection systems, and more. The presence of these technologies can impact the risk assessment.
Analysis of Past Incidents and Claims: A company’s history of cyber incidents can give insurers a good idea of the company’s risk level. Companies with frequent past incidents may be seen as higher risk.
Compliance with Industry Standards and Regulations: Companies that adhere to recognized industry standards like ISO 27001, or comply with regulations such as GDPR, HIPAA etc., show a commitment to cybersecurity, which can favorably impact their risk assessment.
Supply Chain and Third-Party Risks: The insurer might also assess the company’s process for managing third-party risks, such as those posed by vendors, contractors, or service providers.
The results of these assessments form the basis for determining whether to provide coverage and at what cost. The more robust the company’s cyber defenses and the lower the potential financial impact of a cyber attack, the more favorable the terms of the insurance policy will likely be.
Cyber insurance and ransomware
Ransomware attacks have become more common in recent years. Thanks to RaaS (Ransomware-as-a-Service) crime model, criminals can perform these types of attacks easily, even if they don’t have strong hacking skills themselves. Therefore, it makes sense for organizations, especially from the sectors more often targeted by ransomware, like finance or healthcare, to have insurance coverage for losses resulting from ransomware attacks.
According to a 2022 report by Sophos, The State of Ransomware, over four in five mid-sized organizations have insurance against ransomware. However, while 83% of respondents say their organization has a cyber insurance cover against ransomware, 34% say there are exclusions in their policy.
Making the most of your cyber insurance policy
Strategies to maximize the benefits of your policy, including regular system audits, penetration testing, employee training, and incident response planning
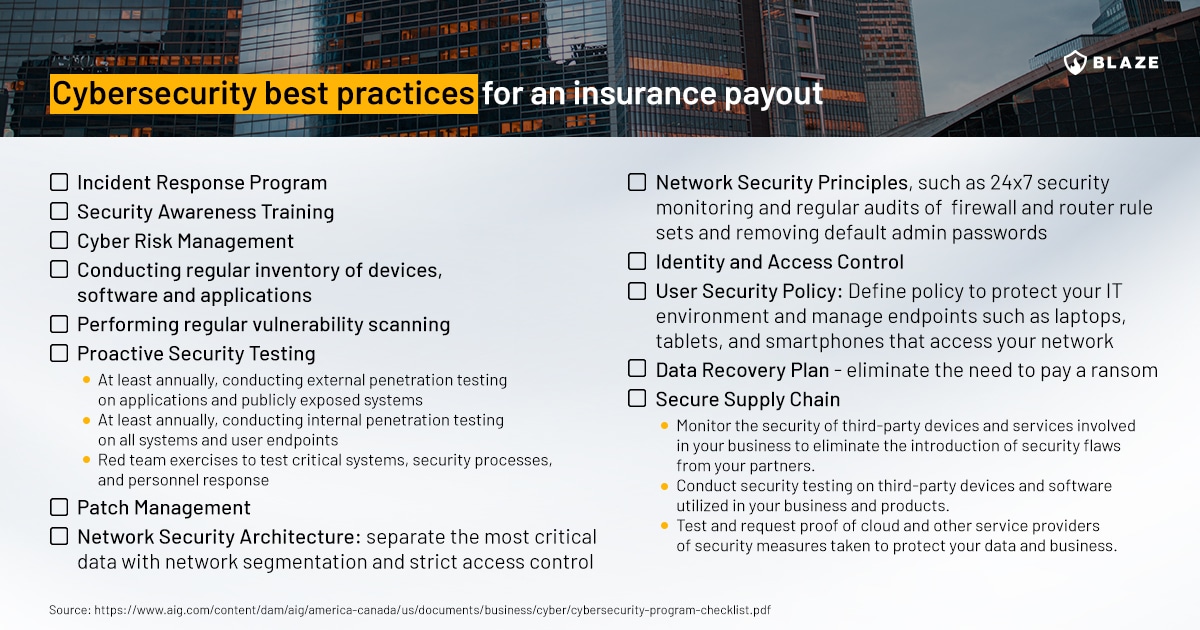
Cybersecurity best practices for an insurance payout
As recommended by AIG:
The future of cyber insurance
The authors of the McKinsey report from 2020 pointed out that the cyber insurance market
still doesn’t cover most cyber risks except customer-data-breach mitigation and regulatory penalties. Direct costs, reputational risks, and intellectual property theft do not get meaningful coverage. Since companies cannot effectively hedge cyber risks, they adopt new technologies relatively slowly for fear of their adverse cybersecurity implications.
A lot has changed since that report, and according to Sophos’s State of Ransomware whitepaper:
- 94% of those with cyber insurance said the process for securing coverage had changed over the last year.
- 54% say the level of cybersecurity they need to qualify for is now higher
- 47% say policies are now more complex
- 40% say fewer companies offer cyber insurance
- 37% say the process takes longer
- 34% say it is more expensive
As the cyber insurance landscape evolves, making coverage harder to obtain, a remarkable 97% of insured organizations have adjusted their cyber defense strategies to better their standing. Among these, 64% adopted new technologies or services, 56% amplified employee training and educational activities, while 52% modified their processes or behaviors.
Summary
Cyber insurance is not a silver bullet but rather a part of a comprehensive cybersecurity strategy – a safety net cushioning the financial blow in the wake of a cyber incident and aiding in the recovery process.
Robust security practices remain your organization’s first line of defense. This includes implementing advanced security technologies, regularly conducting vulnerability assessments and penetration testing, training staff to recognize and avoid threats, and creating a well-planned incident response strategy. These proactive measures not only enhance your organization’s security posture but can also potentially reduce the premiums on your cyber insurance policy.